Most malicious phishing emails work by trying to get the reader to take action (usually either clicking a link to a website or opening an attachment). This is by far the most common tactic we see on a daily basis at AnteSpam.
What does it take to motivate someone to take such a risky action? It depends.
Maybe getting an email from your boss saying everyone needs to click a link to update work info. Perhaps a threatening email with an attachment of the lawsuit being filed against you. Maybe an email congratulating you on winning a million dollars or a brand new iPad. Different people are motivated by different things, and phishers send out hundreds of different kinds of emails every day, in hopes of getting a single click.
With that in mind, let’s look at some of the general categories in which malicious emails can usually be sorted into.
There’s lots of overlap in these categories, but in general, you can break the phishing emails down into seven broad categories.
1. Humor
These malicious emails work by telling a joke to distract the reader from the dangerous link or attachment. Everyone shares jokes online – which means that many people who read these funny emails will automatically consider these emails safe.
In this example, the same part of human nature which America’s Funniest Home Videos banked on – where we find others’ mistakes funny – is used to tempt the reader into clicking the link.
Sometimes the link is supposed to be for a video. Sometimes it will supposedly reveal the punchline. But the link will instead end up putting you in harm’s way.
2. Alarm or Frighten
Ever get an email that made your heart stop because of its serious or threatening message?
Scam emails of this nature can be legal threats (spouse suing for divorce, stranger injured on your property). Or they may pretend to be a notice from law enforcement about legal trouble or that something happened to your family, property, or business.
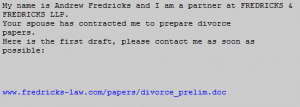
It is relatively common for these emails to be both short and vague. The email instructs you to read the attachment for further details and the answers to the questions surely coming to mind. Or there could be a threat of action unless you fill out a form at a website, just click the link in the malicious email.
Remember that if you are in legal trouble, an email will be the last way that the IRS, police, or a lawyer will try to get in touch with you.
3. Concern
This category of scam email is very similar to the previous one provoking alarm.
These are less dramatic but tend to demonstrate some vague aspect of validity to trick you into thinking it’s a legitimate email.
Types of emails in this category:
- Overdue invoice for an Amazon product
- Notice about service discontinuing if you don’t do X
- Warning about an account (bank, PayPal, etc.) needing information
These emails are more likely to be styled as if they come from the business that they claim to be from. They will often contain logos, colored backgrounds, and maybe even text copied from emails you might actually receive from American Express, Comcast, or AT&T.
Unfortunately, these will have links to malicious sites or dangerous attachments included. If you’re in doubt about their validity don’t click on the link – just visit the businesses website by entering their web address in the browser yourself.
4. Great News
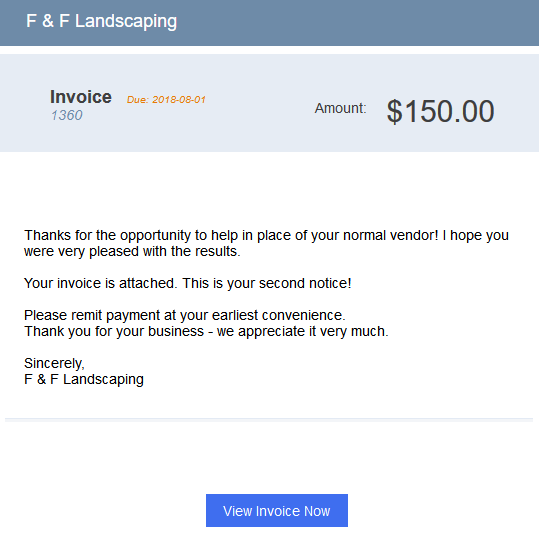
Hey, you won a prize! Isn’t that fantastic?
Wait.
What’s true in life is also true on the internet: if it seems too good to be true, it is very likely dangerous.
Avoid the temptation for easy money or a free prize. If you didn’t do anything to enter a contest, then any contest winnings are likely a lie. Emails with supposedly great news can be malicious emails.
This example also demonstrates that the sender doesn’t necessarily have to convince you to click on just one link. In this email, you have the large red button, but the small text link for the “online version” can add a sense of legitimacy to the email (but you can bet that link is also dangerous).
5. “Normal” Administrative
These can be similar to the Concern category but are distinctly business related.
Commonly we’ll see emails supposedly coming from Human Resources or a boss at work. Maybe you are being told that HR needs to update their files or there is a new email service being used, so you need to register on a specific and unfamiliar website.
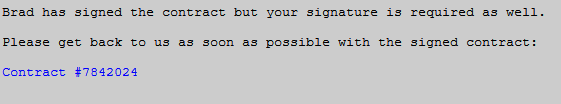
Scammers can and will also scope out a business’s website and input names and addresses into the scam emails! The CEO’s or HR’s contact info are frequently used to give a sense of legitimacy to the message contained.
If you’re in doubt about the legitimacy of an email from a boss or fellow employee, contact them offline to find out if they really sent it.
6. Curiosity
Taking advantage of the old adage “curiosity killed the cat,” these malicious emails can be vague in a way that encourages the reader to click the link.
Often these emails are about an unexpected package delivery or vague news from a friend about something new.
![]()
This method can be particularly effective when a scammer hacks a person’s email account and sends these to people in that account’s contact list.
If you get an email out of the blue (even from someone you know) requesting you to click a link or download a file, make sure that they really sent the email before you click!
7. Social
These phishing emails take advantage of your trust in your friends and family and a social networking service like Facebook, Twitter, Reddit, or many others.
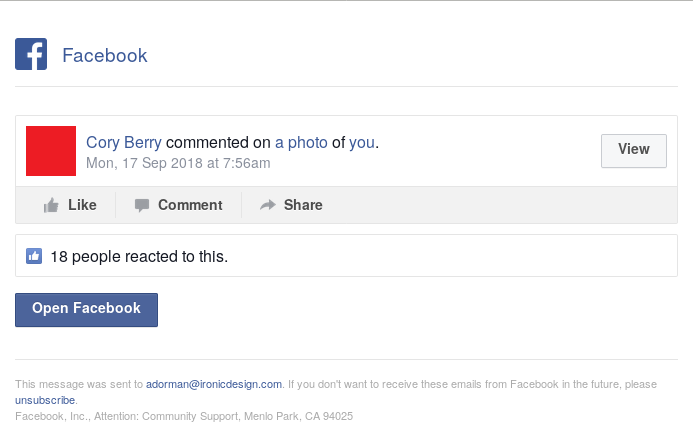
Forging a social networking email to look “normal” is surprisingly simple. It mostly consists of grabbing copies of the typical email images. The hardest part is knowing who to forge for the sender since they should have a relationship with you in order to fool you. However, social network accounts are compromised all the time providing hundreds of credible phishing email target recipients.
Malicious Phishing Email Type Summary
Pretty much any text or email that encourages you to click on a link, open an attachment, or send return info should immediately raise a red flag – especially if it’s unexpected! When you see an email like this, make sure to confirm it is “real” and safe before you take the action requested in the email.
Avoiding falling victim to most of the above emails is simple and easy. Just remember to check a link before you click. Next, do not be fooled by a link with the name of the forged sender near the beginning. For example, http://www.facebook.bus-email.com/ goes to the bus-email.com web site and NOT Facebook.
AnteSpam’s Email Security Training helps familiarize people with these different kinds of email deceptions. It teaches you how to find out whether an email is legitimate or malicious before it ends up costing you thousands of dollars (or more) in time, data, and business lost.




