One of our most innovative and useful products for your business’s security is our Email Security Training.
We’ve spent years helping users filter out junk and malicious emails as part of our Antespam service, but time and time again we’ve noticed that a well-trained user is better than any spam or virus filtering program.
Not only will a savvy user not waste time opening junk email, but there are also threats today that cannot be stopped by even the most advanced and up-to-date spam filtering or antivirus software.
These are called zero-day threats, and these are where your security depends on your users.
Zero-Day Threats Explained
A zero-day threat (sometimes called a zero-day exploit or virus) is the most dangerous kind of threat you’ll find today.
Simply put, a zero-day threat is a vulnerability that is either unknown or unpatched by either software developers or security researchers. Since the vulnerability isn’t known until a virus or exploit is released into the wild, developers have no time (zero days) to fix the software’s code.
While sometimes programmers are caught off guard by zero-day threats, it’s not always possible for a developer to fix his software.
WinRAR’s Vulnerability
If you’ve used Windows computers for any length of time, you’ve probably used (or are familiar with) WinRAR. WinRAR is a Windows utility used to create, view, and extract ZIP and RAR archive files. It can also unpack a wide variety of other archive formats.
WinRAR is an example of a type of program called “nagware.” It’s free to download and use, and while the version contains all the features of the paid application, it will remind you at regular intervals to buy the unlocked version. It won’t stop working, but it will try to annoy you into supporting the developer.
However, it turns out that WinRAR has had a pretty substantial security vulnerability for a majority of its 24-year history.
The vulnerability was severe, since it allowed an attacker to trick WinRAR into importing dangerous malware into a hidden area of a person’s computer. This importing would happen without giving the user any notification that anything was wrong.
You can see this in action in this short 0:36-second video:
To WinRAR’s credit, once the vulnerability was discovered, they patched WinRAR very quickly (removing the offending DLL file) and also sending out an email to all the licensed WinRAR users about the vulnerability and encouraging users to update immediately.
If you do have WinRAR and you haven’t updated before April 2019, go do that now. The first patched version is 5.70 beta 1.
A Success Story…Almost
This would be a great example of how these kinds of massive vulnerabilities should be patched, except for one small problem.
WinRAR has about 500 million users. While I don’t know how many of them paid for the software, I think it’s fair to assume that a lot of those users are still using the free version and dealing with the nagging.
Another portion may have paid, but either put in a junk email address or no longer check the email address that they used to register WinRAR.
Finally, and maybe the biggest problem is WinRAR does not contain any mechanism to support automatic updates or notifications encouraging users to update.
This combination of factors makes WinRAR’s vulnerability – which has been discovered and patched by developers – into a virtual zero-day threat since a (potentially large) portion of those 500 million users will likely never know about or be forced into an upgrade.
Unless…
This kind of situation is why you train your users.
No antivirus, spam filter, or program is 100% safe. New zero-day attacks are being discovered and used all the time.
And right now, attackers know that this WinRAR vulnerability exists and that there are likely 10s or 100s of millions of users and computers vulnerable.
All it would take to have your security compromised and have your network locked down by ransomware or have your user’s or customer’s confidential information stolen is one untrained user opening up a malicious file with WinRAR.
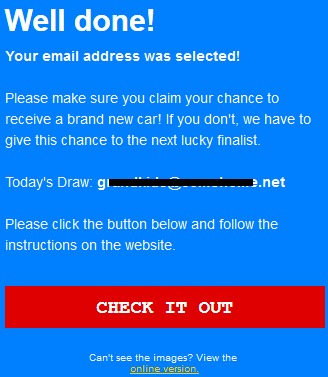
If you haven’t spent any time educating your users on how to spot potentially dangerous emails, you should.
And while you can spend days in the classroom, Antespam Email Security Training teaches users right in their inbox in under a minute. A free month-long trial is available, so you can try it with no risk.